How to get a Finnish IP address
The easiest way to improve your digital privacy is to switch your IP address using a VPN. We’ll …
You’ve probably had your fair share of emails from companies like Yahoo, Marriott, Quora, Equifax, and more, stating that your login credentials may have been breached. But what exactly happens when a giant data breach occurs, and do people even care when they get these emails? Well, due to a technique called “credential stuffing”, data breaches are far more dangerous than you might think — and you definitely shouldn’t just delete the emails and assume nothing will happen to you.
When a data breach occurs, the information stolen generally gets put in a database. Cyber criminals then attempt to sell that database on the dark web. Often, the information eventually leaks onto the open internet, which means it is then accessible to anyone with a computer for free.
Credential stuffing is a relatively new technique for
Reddit acknowledged that this act of ‘credential stuffing’ is causing a lot of trouble right now. Basically, if you use the same email and password for most of your accounts, a hacker can use credential stuffing to access them all and steal your credit card details, rob your bank account, buy things in your name, and generally reak havoc on your financial life.
This practice is dangerous to both companies and consumers, and it has become one of the most common ways to take over an online account.
Here’s how credential stuffing attacks work:
One of the main reasons credential stuffing works so well is that many people use the same passwords from one account to another. If you, for instance, use the same password for your Facebook account and your bank account, if a hacker gets access to your Facebook page using credential stuffing, what’s stopping them from accessing your bank? Nothing. And the software takes away the heavy lifting making it effortless for a cyber criminal.
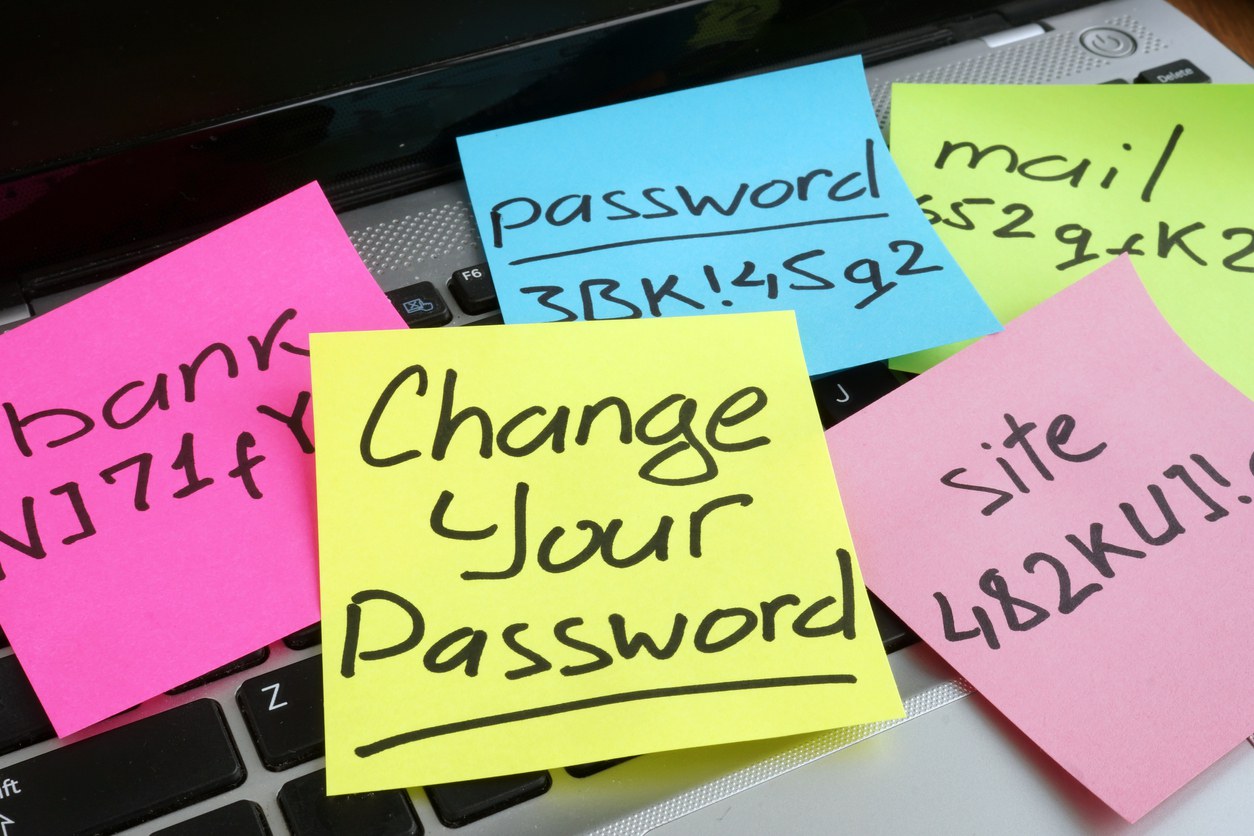
To get everything under control, you need to use unique, difficult to guess passwords for every account. One way to do that is with a password manager.
A password manager will automatically fill in passwords for sites you visit, and you control it with a single ‘master’ password. This means you can have unique passwords for each site, but you don’t need to remember them all. That’s what the app does. You just need to remember your master password.
You might wonder what the difference is between a password manager and the way web browsers offer to save and store you passwords. With a browser, the information is not encrypted, so scammers can get access to it.
The most important thing to remember is to choose a difficult to guess ‘master’ password. This password must be random, like “HG92^9smbo*HA@”. If you’re not using a password manager, you should create a unique password like this for each and every account you have. This prevents
So remember: Don’t just delete that data breach alert email and assume nothing will happen to you. With credential stuffing, all of your accounts could now be at risk.
Techniques like credential stuffing are some of
